Why Threat Modeling is Crucial in DevSecOps
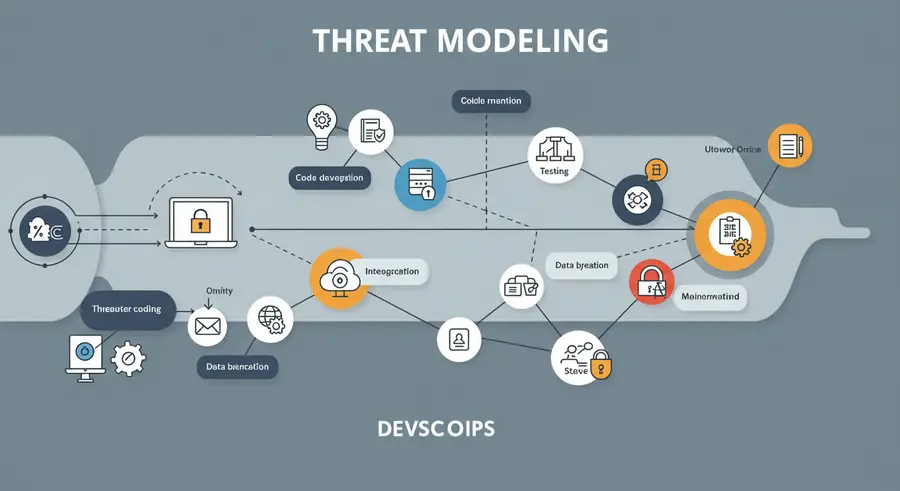
In the dynamic world of software development, simply reacting to security vulnerabilities after they emerge is a costly and often ineffective strategy. DevSecOps champions a shift-left approach, embedding security into every phase of the Software Development Lifecycle (SDLC). At the heart of this proactive philosophy lies threat modeling, a structured process for identifying, analyzing, and mitigating potential security threats early in the design and development phases.
Threat modeling helps teams anticipate where attacks might occur, understand their potential impact, and design appropriate countermeasures before a single line of code is written. It's not just about finding flaws; it's about understanding the system's security posture from an attacker's perspective, fostering a security-aware culture across development, operations, and security teams.